When using AWS Direct Connect to communicate with a region, AWS recommends the architecture shown in the following figure for production workloads to ensure maximum resilience:
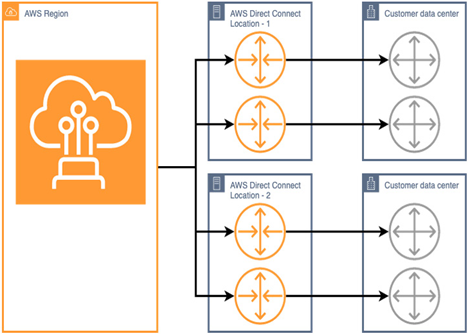
Figure 6.14 – AWS recommendation for maximum resilience with Direct Connect
At the time of writing, only the AWS Local Zone in Los Angeles has more than one availability zone in a similar fashion to a region. In situations such as this, the recommendation should be followed.
However, most AWS Local Zones are single logical entities. Further complicating this, the number of AWS Direct Connect Locations situated within a given AWS Local Zone’s metro area varies. For example, Las Vegas has two AWS Direct Connect locations—SUPERNAP 8 and Databank LAS1. Helsinki, on the other hand, has only one—Equnix HE6. It would simply not be possible to implement this recommendation while retaining single-digit millisecond latency and data sovereignty across both locations—one of the locations would need to be in a different country entirely.
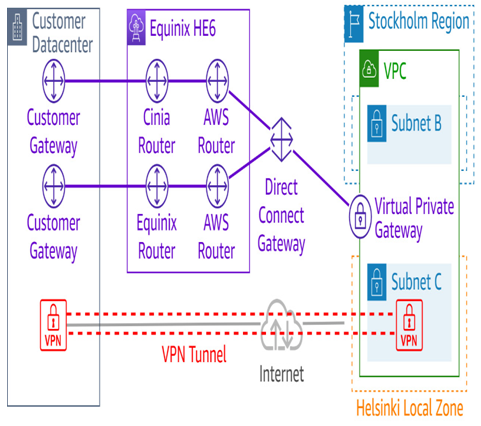
Figure 6.15 – Augmenting resilience to the AWS Local Zone in Helsinki
This figure gives examples of what could be done to maximize the resilience of connectivity in this situation. It is not uncommon for customers to run VPN server endpoints on EC2 instances such as this in AWS Local Zones, not only for resilience but also as a service they offer their customers.
Check the AWS Direct Connect Locations page on the AWS website for the latest information on availability in the area you are interested in.
Media Access Control Security (MACsec)
Media Access Control security (MACsec) is a protocol designed for Ethernet-based networks. Implementing MACsec in the context of AWS Direct Connect presents several benefits:
Data confidentiality: MACsec encrypts packets at layer 2 (the data link layer) before they traverse the Direct Connect link. This ensures that data remains confidential while in transit, protecting sensitive information from eavesdropping or interception.
Integrity and authenticity: MACsec not only encrypts the data but also authenticates it. This means that data cannot be tampered with during transit without detection. By ensuring both the integrity and authenticity of packets, users can trust that the data they receive is the exact data that was sent, untampered and from a legitimate source.
Protection against replay attacks: MACsec incorporates an anti-replay mechanism, which prevents malicious actors from capturing valid data frames and re-sending them. This ensures that old or previously captured data cannot be used maliciously to impersonate valid transmissions.
Enhanced security posture: By integrating MACsec with AWS Direct Connect, organizations can bolster their overall security posture. The protocol complements other security mechanisms, such as VPNs and TLS, ensuring a layered security approach. While higher-layer protocols secure data at the application or transport layers, MACsec adds another layer of protection at the data link layer.
Transparency: Since MACsec operates at layer 2, it’s largely transparent to higher layers in the networking stack. This means that applications and services running over Direct Connect don’t need modifications to benefit from MACsec’s security enhancements.
Low latency: Encryption at the data link layer is efficient and introduces minimal latency. This ensures that the high-speed, low-latency benefits of Direct Connect remain largely unaffected, even when adding robust security features.
Compliance: For organizations subject to stringent regulatory requirements related to data protection, incorporating MACsec can aid in compliance efforts. Ensuring data in transit is encrypted and tamper-proof can be a critical component of regulatory standards.